Support organizations in the security of sensitive data. Data, such as customer data, design data of (new) products / services or data that fall under the privacy legislation (GDPR), examples of data that your organization does not like to go public or worse. Yet more and more cases of data theft are known. You may think that your sensitive data is completely protected against theft by anti-virus software, security scanners or a firewall, unfortunately this is not the case.
Monitor important or sensitive data in real time and alert when this data is being accessed in potentially inappropriate ways. For example, alert when a user, who does not need to, accesses the sensitive data. Ransomware that will pack your files will be immediately stopped.
Keep an eye on (external) management tasks, to ensure that a possible data breach does not occur from the inside or through the actions of third parties working on behalf of your organization. Also assist with discovering Trojan Horses (malware hidden in an application) in your network. Form a second detection layer and alert when the antivirus software failed in detecting the Trojan.
First time installed? You can login by using a web browser like Internet Explorer or Firefox and go to: https://<Server-IP>/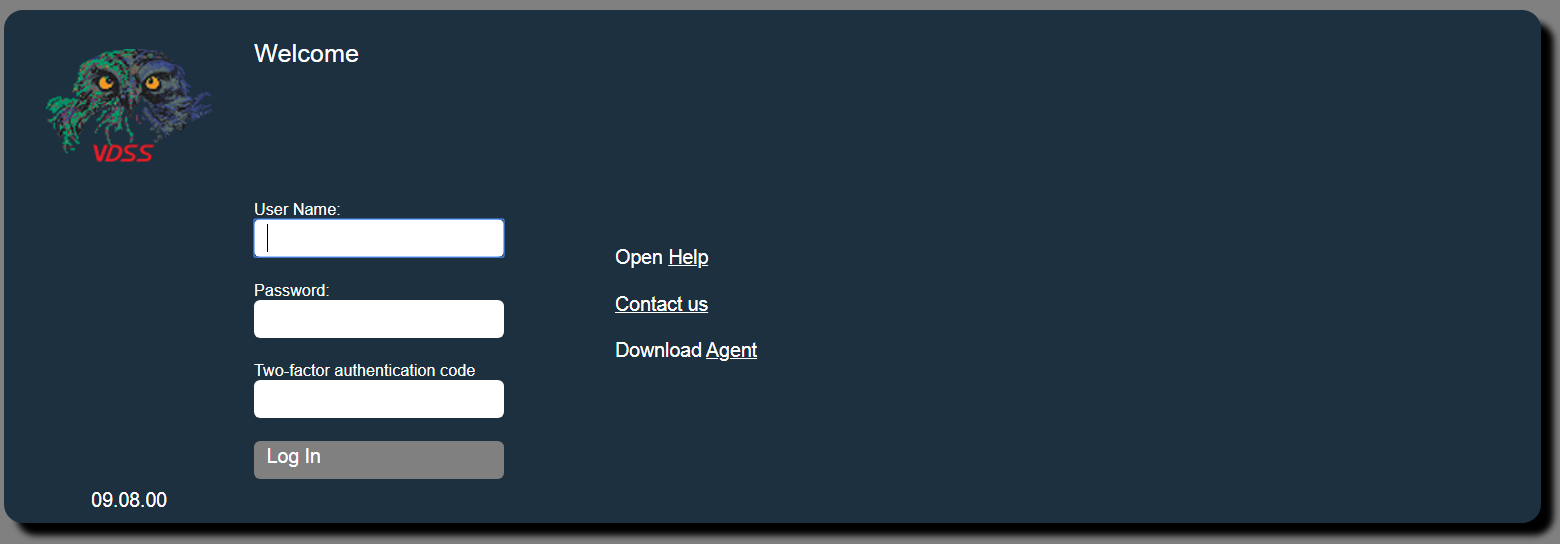
You can login with User Name: firstlogin and Password: Firsttime123
Two-factor authentication will ask you to activate if it is required or optional.
If you already have your own account then you can use that.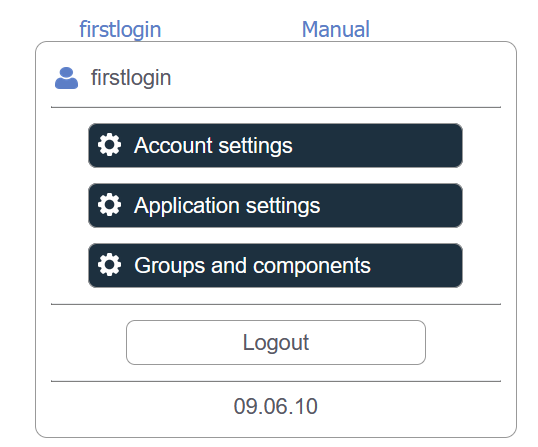
Your accountname will appear in the upper right corner. To change your settings click here
Next your account name is the Manual. Click on the manual and an extra window will open with the manual
There are several menu options, depending on your rights. Some users can only see the "Show" menu for example.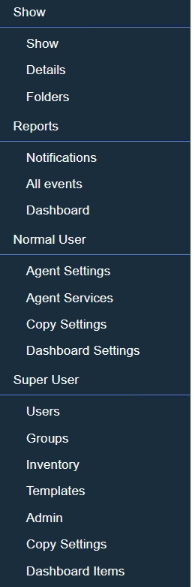
•Show: overview of the status of all components
•Reports: overview of all current notifications, provides comprehensive and integrated reporting for all data collected and stored in the system and show dashboard items (also connect to external applications) in a central Dashboard
•Normal User: configure the monitoring for systems you are monitoring
•Super User: administrator rights within the application