Hackers Selling Access and Source Code From Antivirus Companies
Bron: Bleepingxcomputer
A hacking group or individual is advertising access to the networks of at least three antivirus companies in the U.S. and source code for their software products.
The initial asking price was $250,000 for access information and $150,000 for the source code but they were ready to sell both for at least $300,000 depending on the antivirus company the buyer is interested.
This offer was for each individual company and it is not a set price. It could go as high as $1 million for one access. A definitive offer is still being discussed with intermediaries.
Claiming 30 terabytes of stolen data
In March, an actor calling themselves Fxmsp announced to members of criminal underground communities that they could provide exclusive information stolen from major antivirus companies located in the U.S.
In late April, Fxmsp said that after hard work through the first quarter of 2019 they managed to breach the companies’ networks and had secure long-term access.
They offered screenshots of folders that supposedly contained 30 terabytes of data, claiming it was extracted from the breached networks.
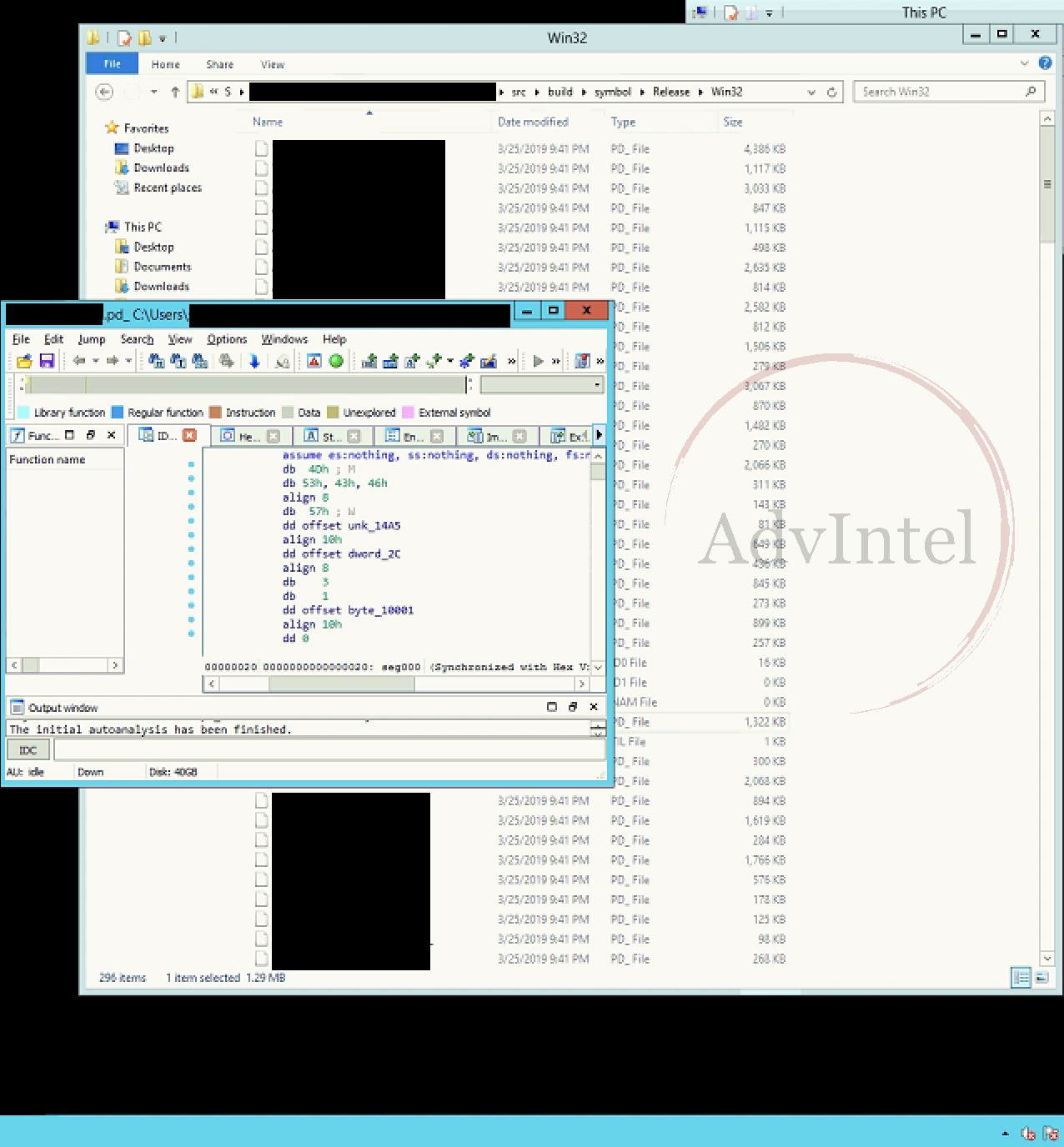
“The folders seem to contain information about the company’s development documentation, artificial intelligence model, web security software, and antivirus software base code,” security company AdvIntel says in a report released today.
Yelisey Bogulsavskiy, AdvIntel’s director of security research, told BleepingComputer that Fxmsp reportedly compromised the Active Directory (AD) of at least one company and established persistence through an external Remote Desktop Protocol (RDP) server.
AD is the most critical part of a Windows network, as the server is responsible for authenticating and authorizing all users and computers on the network; it is also where security policies are defined for all the systems it manages.
This tactic has been used by the Carbanak gang against banks across the world. It was discovered by Kaspersky threat researchers at a bank in Russia.
According to Bogulsavskiy, Fxmsp named three of its victims and claimed that they had compromised a fourth antivirus firm, but did not disclose its name.
Actor goes dark, resurfaces with goody bag
“The actor claimed that antivirus breach research has been their main project over the last six months, which directly correlates with the six-month period during which they were silent on the underground forums where they normally post,” says AdvIntel.
According to the New York-based fraud prevention company, Fxmsp disappeared from underground forums in October 2018 and returned in April this year.
Fxmsp appears to be a hacker group that speaks both Russian and English. They are specialized in targeting corporate and government networks across the globe. In a post in February 2018 we found on an underground forum, the actor advertised access to the corporate networks of a company, which included account entries for all employees, “from cleaners to the president.”

Monetizing access data is done via proxy sellers that attract buyers from both Russian and English criminal forums. Although they sell only to one buyer, Bogulsavskiy told us that Fxmsp is known for secretly re-selling their “goods.”
The activity of the individual(s) behind the Fxmsp alias is known among infosec experts. FireEye mentioned them in its 2018 e-crimes report for the EMEA (Europe, the Middle East, and Africa) region.
On April 5, 2018, Fxmsp advertised access information for the network of a hotel chain with locations in Europe, Africa, and South America.
AdvIntel believes that Fxmsp is a credible hacker collective that sells verifiable corporate access. The researchers believe that the group turned a profit of about $1 million by now. Other offers from Fxmsp include network access for the following businesses:
The actor seems to be active since at least 2017 and assumed a stolen identity of someone named Andrey Turchin to carry out their business. We were told by someone with knowledge about this actor that this identity is that of a real person. Although it is burned at the moment, this shows the level of sophistication this actor has.
